- Get link
- X
- Other Apps
- Get link
- X
- Other Apps
Image Credit: Gerd Altmann from Pixabay
We are going to see three different types of spams or likely spams in this case.
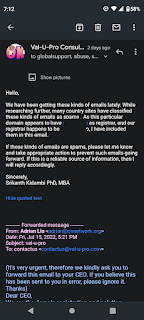
First one is the "Domain" spam. What is a "Domain" spam?
As per global reports around the world, this is a spam where someone sends an email similar to the one shown below claiming that the organization is a registrar in the mentioned country, and they are looking into preventing an organization trying to register a domain in the mentioned country with the same name as the recipient. In this case, the email was addressed to the CEO of VAL-U-PRO.COM, Dr Srikanth S Kidambi, a unique consulting firm that values knowledge and human (independent of race, sex, gender and more) capital to the fullest.
What did we do?
We performed a thorough research on whether similar such email based spams were mentioned in the public media. As expected many countries had pointed out such spams for years in their media outlets. Please see for examples.
===========================================
Published in Canada
"Guarding Against the Chinese Domain Name Email Scam, March 8, 2019
Cyber Alert - Risk Management Question
The Canadian Trade Commission recently issued a warning about a new email"
====================================================
Published in Portugal
Beware this domain name scam originating from China. | Safe Communities Portugal
Home / Cybercrime Alerts / Beware this domain name scam originating from China.
Beware the following email originating from John Liu <chinaregistry177 (at) aliyun.com address individually to you. It is a scam trying to get you to part with your money. The website at the end of the message does not exist.
Subject: CN Domain and keyword
“(It’s very urgent, please transfer this email to your CEO. Thanks)
======================================================
Published in Indian media Outlet in Late 2021
Beware of China Domain Name Registration Scam, Ignore Mails from .cn Mentioning Domain Conflict
China domain name registration scam, which was first reported around the year 2010, is still being carried out by fraudstersChina domain name registration scam is still being carried out by scammers. Although the scam was first reported in 2010, the fraudsters behind it are still finding a way to try and mislead gullible viewers into paying for a domain name that is not needed. While this scam has been widely reported and also has a Wikipedia page on it, not many people seem to be aware of how it works.
========================================================
After performing our initial research, we also tried to identify the source for this spam. Upon researching further, we identified the registrar where this domain name was registered. Then, we contacted this registrar through their abuse@registrardomainname.com. Based on our prior experiences notifying for similar such situations where nothing happened, this time we included our registrar and also ICANN, who believe in "One World, One Internet", part of the email communication.
Why did we include ICANN?
ICANN is the oversight board that looks into assigning license for registrars for them to offer domain related services. We felt that they are supposed to know these kinds of happenings as this seems to be a repeated pattern for years.
What is the point in including all these involved parties?
We are always against such spams, if it were to be spams, and would like to prevent such happenings. But, we also considered the "What If" situation namely, what if the email sender is a genuine domain reseller, who is trying to address trademark concern early on in the process. For that reason, we felt that including all these parties might address the issue faster (hopefully). If their findings suggest that this company who tried to reach us is genuine, then we can look into addressing the trademark infringement concern over in China. Moreover, if this were to be true, this is somewhat assuring that China is looking into address their relatively questionable reputation in the IP area.
Please see below is the exhibit II, our email to these connected parties.
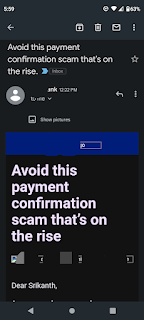
SECOND TYPE OF SPAM - "PAYMENT SPAM"
This email about a payment spam came from a bank. This spam revolves around someone appearing to be from a bank reaching out claiming that a payment is due. If an individual falls for the spam, then they might lose out not only with respect to the payment amount, but also end up losing their personal details, and more.
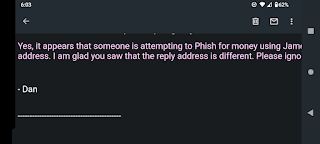
THIRD SPAM - PHISHING FOR MONEY
This one could be a tricky one. This is a spam where someone with an email address that looks very similar to someone who might be in your contact list (for example, xyzlau.com could be used instead of xyzlaw.com) could reach out seeking a favor. In this case, the email address was almost identical except for the last alphabet.
As soon as we noticed this discrepancy, we reached out to our contact and verified whether this email was sent out by this person. As expected, it was not sent by the contact, but ended to be spoofing of the email address by someone else who had access to this email communication. In this day and age, there are various outlets for such kind of information leaks, and we are looking into ways to enhance the overall system.
- Get link
- X
- Other Apps